WHAT ARE THE REQUIREMENTS OF ISO/IEC 27001:2022 CERTIFICATION?
In an era of rising cyber threats, data breaches, and strict regulatory demands, protecting sensitive information has become a top priority for organizations worldwide including those in Qatar’s dynamic sectors such as oil & gas, finance, construction, government, and healthcare.
ISO/IEC 27001:2022 is the latest international standard for Information Security Management Systems (ISMS). It provides a systematic, risk-based approach to managing information security, ensuring confidentiality, integrity, and availability of data.
This guide explains the key requirements of ISO/IEC 27001:2022 certification and how your organization can meet them.
What Is ISO/IEC 27001:2022?
ISO/IEC 27001:2022 specifies the requirements for establishing, implementing, maintaining, and continually improving an ISMS. The 2022 version introduces a refreshed set of controls (reduced from 114 to 93) while keeping the core management system structure largely consistent with the 2013 edition. It aligns better with other management system standards and addresses modern risks such as cloud services, remote work, and threat intelligence.
Certification demonstrates that your organization has a robust framework to identify, assess, and treat information security risks effectively.
Core Requirements of ISO/IEC 27001:2022
The standard is built around Clauses 4 to 10 (the mandatory requirements) and Annex A (reference controls). Here is a breakdown:
Clause 4: Context of the Organization
- Understand internal and external issues that affect your ISMS.
- Identify the needs and expectations of interested parties (e.g., customers, regulators, partners).
- Define the scope of your ISMS.
- Establish, implement, maintain, and continually improve the ISMS, including processes and their interactions.
Clause 5: Leadership
- Top management must demonstrate commitment and accountability.
- Establish an information security policy.
- Assign roles, responsibilities, and authorities for information security.
- Ensure the ISMS is integrated into business processes.
Clause 6: Planning
- Conduct risk assessment and risk treatment.
- Set measurable information security objectives and plan how to achieve them.
- Plan changes to the ISMS in a controlled manner (new emphasis in 2022).
Clause 7: Support
- Provide necessary resources, competence, and awareness.
- Ensure effective communication.
- Maintain documented information to support the ISMS.
Clause 8: Operation
- Implement and control the processes needed to meet information security requirements.
- Execute the risk treatment plan.
Clause 9: Performance Evaluation
- Monitor, measure, analyze, and evaluate the ISMS performance.
- Conduct internal audits.
- Perform management reviews (with added focus on changes in interested parties’ needs).
Clause 10: Improvement
- Identify nonconformities and take corrective actions.
- Continually improve the suitability, adequacy, and effectiveness of the ISMS.
Annex A: Information Security Controls Reference
Annex A lists 93 controls grouped into four domains (reference only you select applicable ones based on your risk assessment):
- Organizational controls (37 controls): Policies, roles, supplier relationships, etc.
- People controls (8 controls): Screening, awareness, terms of employment.
- Physical controls (14 controls): Perimeters, entry controls, equipment security.
- Technological controls (34 controls): Access control, cryptography, secure coding, cloud services, data masking, etc.
You must create a Statement of Applicability (SoA) that justifies which controls are included or excluded.
11 new controls were added in the 2022 version, including threat intelligence, information security for cloud services, ICT readiness for business continuity, data leak prevention, and secure coding.
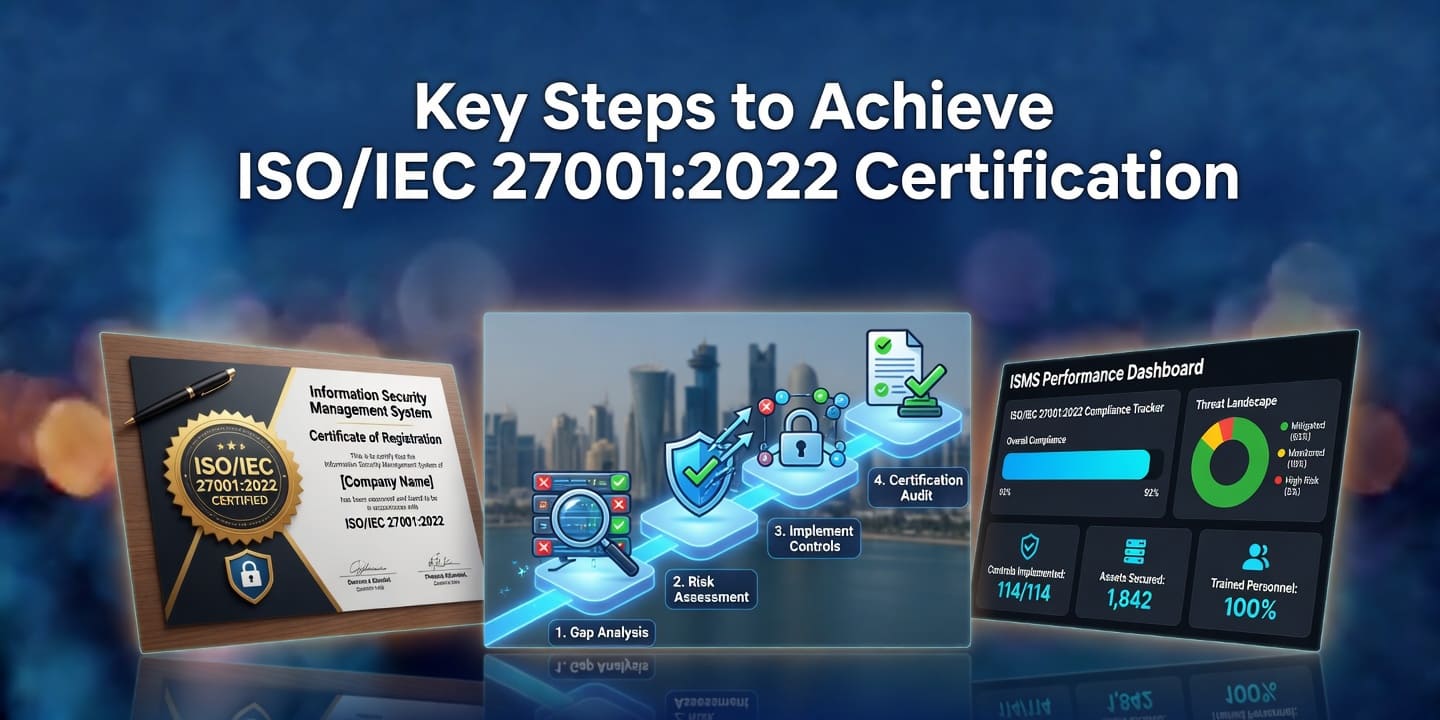
- 1. Define the scope and context of your ISMS.
- 2. Perform a gap analysis against the standard.
- 3. Conduct a formal information security risk assessment and treatment.
- 4. Develop policies, procedures, and controls.
- 5. Implement the ISMS and provide training.
- 6. Carry out internal audits and management reviews.
- 7. Engage an accredited certification body for Stage 1 (documentation review) and Stage 2 (implementation audit).
Why ISO/IEC 27001:2022 Matters for Businesses in Qatar
With increasing digital transformation and regulatory expectations in Qatar, ISO 27001:2022 helps organizations strengthen cybersecurity posture, build client trust, meet tender requirements, and support Qatar National Vision 2030 goals around digital economy and innovation.
Related reads:
Ready to Strengthen Your Information Security?
Implementing ISO/IEC 27001:2022 is a strategic investment that protects your data assets and enhances business resilience.
QAC is the QGOS-approved ISO certification body in Qatar, offering expert support for ISO/IEC 27001:2022 and other standards. Our local expertise ensures a smooth and effective certification journey tailored to Qatar’s business environment.
Contact us today for professional guidance, gap analysis, or to begin your ISO 27001:2022 certification process. Secure your information secure your future.